Background
Peter Jones, Cyber Badger and CIISec, discussed Digital Forensics, Preparation and Response during this month’s SWCSC Networking Meeting.
What is Digital Forensics?
-
- It is the recovery and investigation of material found in digital devices, usually computer crime.
- Looking for specific data within files, e.g., images within files (indecent and criminal), password or code within text
- Includes: Hexidecimal, Progress Bars
5 Stages of Digital Forensics:
-
- Identification – identify what we want (asset register)
- Preservation – preserve what we want (incident response)
- Analysis – analyse and investigate
- Documentation – write notes: time, date, the process and what we did / discovered (incident response)
- Presentation – present findings and evidence
ACPO Principles:
-
- No action taken by law enforcement agencies, or their agents, should change data held on a computer or storage media which may subsequently be relied upon in court.
- In exceptional circumstances, where a person finds it necessary to access original data held on a computer or storage media, that person must be competent to do so and to be able to give evidence explaining the relevance and the implications of their actions
- An audit trail or other record of all processes applied to computer based electronic evidence should be created and preserved. An independent third party should be able to examine those processes and achieve the same results.
- The person in charge (OIC – Officer in Charge) of the investigation has overall responsibility for ensuring that the law and these principles are adhered to.
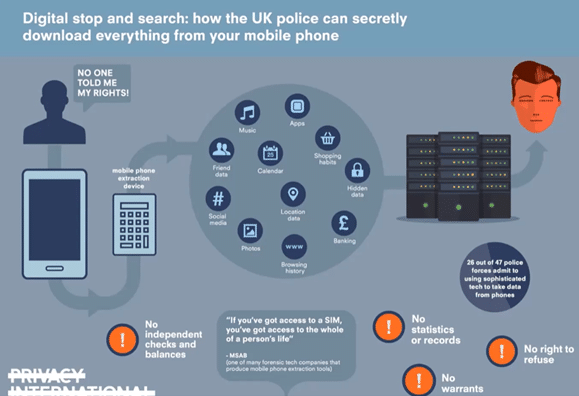
Digital Stop and Search
Remember the following:
-
- Make sure your asset register is up to date.
- Ensure your incident response procedures including the preservation of data.
- Investigations can and usually will last longer then the whole incident response process.
- Communication is key.
- Transparency is even more key.