Background
During July’s SWCSC Networking Meeting, Peter Jones “The Cyber Badger”, Head of Security and CISO, discussed the compliance during a cyber-attack.
Who’s threatening who? We want to know who and what is the actual target to our business
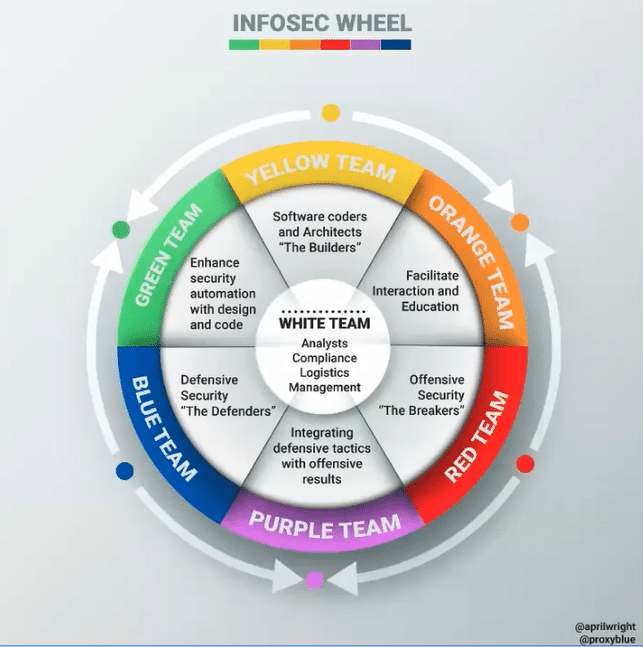
Technical people always jump on the IT solution instead of policies and procedures, whereas those who are Governance specialists will jump on the policies and procedures and then align this to the relevant technologies.
It is important to know what is going on in all the different departments so that they can work together – need to understand these areas to protect the data and critical assets.
Need to have a Business Continuity/ Disaster Recovery (BC/DR) plan for when things “go wrong” – when an incident occurs it is essential to have procedures and a plan in place to resort to when in a crisis.
SANS podcast: Cyber Insurance is seen to be pretty much “worthless” in some areas since they do not have enough protection to cover the ransomware repercussions.
“Compliance is just a tick box exercise?”
- Wrong – the reality is that so many feel that compliance is a means to an end
Compliance – Adoption of Best Practice?
Using Compliance to your Advantage
-
- Findings are good
- Opportunities for improvement are great
- Continual improvement is amazing
- The art of driving best practice to drive policies, procedures and exercises that are best suited to your organisation – not that of a template downloaded from the Internet
Identify the framework that works best for YOU (some of these frameworks compliment each other, for example, Cyber Essentials controls can be mapped to ISO 27001 controls)
-
- ISO 27001
- NIST Cyber Security Framework
- Cyber Essentials scheme
- COBIT
- SOC
Spirit of Crisis
-
- Select a number of likely scenarios
- Test them against your organisation’s security
- Technical, People, Process
- What remediation is needed now to stop further problems?
- What are the blockers?
- Measure the successes and failures
- No blame – remediate!
Scenarios